
Let’s continue stepping through my eight predictions for 2021! So far, we’ve covered why ransomware victims will face penalties, how your digital reputation will come under attack and why Zerologon will continue to cause pain for IT pros. Today, it’s time for prediction #4: People will remember the hard way that they have Group Policy.
Three key things to understand about Group Policy
Let’s start with a brief refresher of the three critical things you need to know about Group Policy.
1. It’s immensely powerful.
Group Policy is a key feature that’s built into Active Directory. It enables administrators to set limits on what can and cannot be done across the IT environment. They can create settings for both users — from business users to administrators — and computers — from user endpoints to AD domain controllers. In fact, Microsoft’s Reference Spreadsheet lists literally thousands of settings.
Here are just a few of the things you can do with them:
- Establish and enforce password policies.
- Prevent the use of removable media drives, which are a vector for malware infections.
- Restrict access to the command prompt, so users can’t run unauthorized code.
- Block users from installing new software on their systems.
- Disable NTLM authentication, which is weaker than the more modern Kerberos authentication.
- Prevent Windows from storing LM password hashes, which are fairly easy to hack.
2. It’s often neglected, misused or overlooked.
All too often, though, the power of Group Policy is not sufficiently respected, and it is not given its proper due in the organization’s security strategy. At many companies, it is treated as a set-it-and-forget-it technology —it was configured a long time ago and has gone largely untouched ever since. This “out of sight, out of mind” attitude is like a flashing “Welcome!” sign to malicious actors.
Some organizations go to the other extreme: They use GPOs liberally, creating them as a quick fix for every little thing that they need. Over the years, they have amassed hundreds or thousands of GPOs, and no one has the faintest clue about how to make sense of them. In all that clutter and the noise of constant changes, who’s going to notice if someone quietly alters a setting or two for their own nefarious purposes?
3. Attackers don’t need much skill to hack it.
Group Policy is part of every Active Directory environment, so bad actors don’t have to develop a new attack playbook for each organization they want to infiltrate. They can simply re-use techniques they’ve perfected (and shared with each other) over the years.
Moreover, once an attacker gets in, they don’t need much technical know-how at all to tweak just the right settings to get what they want. Why not? Well, there’s actually an open-source tool called BloodHound that reveals all the privilege relationships in an Active Directory environment. It was designed to help legitimate IT specialists improve security, but there’s nothing to stop hackers from using it too. Simply by running BloodHound, a malicious actor can get a detailed map of the exact attack paths they can use to stealthily conduct reconnaissance and gain elevated access rights until they are ready to steal your data, disrupt your operations or achieve some other end goal.
The vital importance of Group Policy in 2021
If you read my third prediction about why Zerologon will continue to cause pain for IT pros, you already have one clear example of why IT pros are going to need to pay closer attention than ever to Group Policy in 2021. Using the Zerologon vulnerability, and attacker can gain access to one of your domain controllers — which means they can change your GPOs however they please. As we’ve just seen, that gives them enormous power over your entire domain.
Take another look at the examples I gave earlier of some of the things you can do with Group Policy. They are all consistently featured in “top 10” lists of the most important GPOs to configure for security. Now consider what would happen if someone altered just a few of those GPOs — for example, they disabled your password policies and allowed users to install unapproved applications on their computers. Suddenly, you could find yourself with not just one hacker in your environment, but user (and admin!) credentials being compromised every second and malware running rampant across your entire IT ecosystem.
Simplify Active Directory GPO management and governance
How to harden your security
So, what can you do to defend yourself? To be blunt: Make Group Policy a central part of your security strategy! For starters, get deep insight into what GPOs you have. In particular, you want to spot redundant or conflicting settings and clean them up. (This is especially important if your organization has been in the “long-term GPO proliferation” camp rather than the “set it and forget it” camp.)
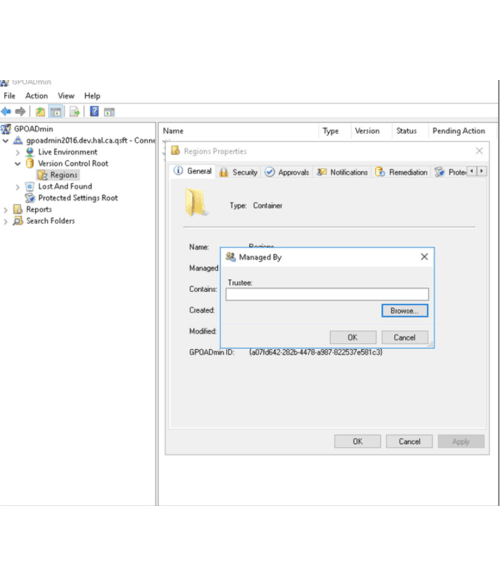
Next, you’ll want approval-based workflows that help ensure all changes are both authorized and accurate. After all, a fat-fingered admin can bring down your IT operations or open you up to a security breach just as quickly as an attacker can. For even more protection, it’s enormously helpful to be able to assign responsibility for specific policies to specific admins, so no one can accidentally or deliberately step on settings they’re not responsible for.
Finally, of course, you also need to know right away about changes to your GPOs and be able to quickly revert back to known-good settings if a GPO change is unauthorized or has an undesired effect. Even better, you want to be able set some GPO values in stone and prevent them from being modified in the first place.
Stay tuned…
In my next blog post, I’ll take a deep dive into my fifth prediction: With mergers and acquisitions on the rise, more people will realize just how hard a tenant-to tenant migration really is. I promise, you won’t want to miss it!



