In the last entry posted to this blog , I described the mechanisms (including PUNC bits and commit log sequence numbers, aka CLSNs) used by Db2 for z/OS for lock avoidance purposes (lock avoidance here refers to a capability whereby Db2 can, in many cases, verify the committed state of a data value without having to get an S-lock – i.e., a read lock – on the page or row in which the value is located). As lock and unlock requests consume CPU cycles, lock avoidance is a CPU efficiency booster for Db2 …read more
Related Articles

Using Extended Events in Azure
Over the past 6 months I have been trying to push myself to use extended events (XEvents) over SQL trace, once you get past the learning curve it’s probably the way to go. If you are operating in the ...
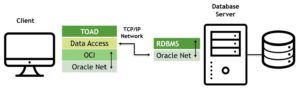
Getting to Know the Three Methods of Connecting to the Database Using...
In this article we are going to learn the three ways in which we can connect to our Oracle database using Toad for Oracle. First of all, in order to work with this tool, we need to have Oracle databa...

Toad Data Point wizards make data preparation easier
Data preparation makes it possible to extract accurate insights from data analysis for business use. Developing those insights requires connecting multiple data sources and ensuring the data is clean ...
