In the last entry posted to this blog , I described the mechanisms (including PUNC bits and commit log sequence numbers, aka CLSNs) used by Db2 for z/OS for lock avoidance purposes (lock avoidance here refers to a capability whereby Db2 can, in many cases, verify the committed state of a data value without having to get an S-lock – i.e., a read lock – on the page or row in which the value is located). As lock and unlock requests consume CPU cycles, lock avoidance is a CPU efficiency booster for Db2 …read more
Related Articles

How to append to datasets in Toad Intelligence Central
This video shows how to append to datasets and files in Toad Intelligence Central....
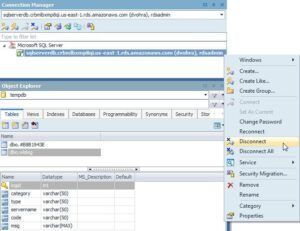
Using Toad for SQL Server with AWS RDS
Introduction Toad for SQL Server is an integrated development environment (IDE) for accessing, administering and using SQL Server. The SQL Server may be on a local machine or may be on a remote platf...
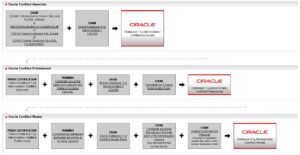
Why Certifications Are Important
Introduction Ever since I started my career in Oracle technology I’ve always wanted to deliver the best support to my clients. I have wanted to solve the problems quickly. I am not afraid of new chall...
